SolarWinds Cyberattack Prompts Calls for Aggressive Countermeasures
WASHINGTON — A congressional hearing Friday showed that foreign computer hackers are facing a growing likelihood of counterattack from the United States as a result of the SolarWinds software breach.
Lawmakers and computer industry officials agreed the hackers must face consequences to deter them in the future.
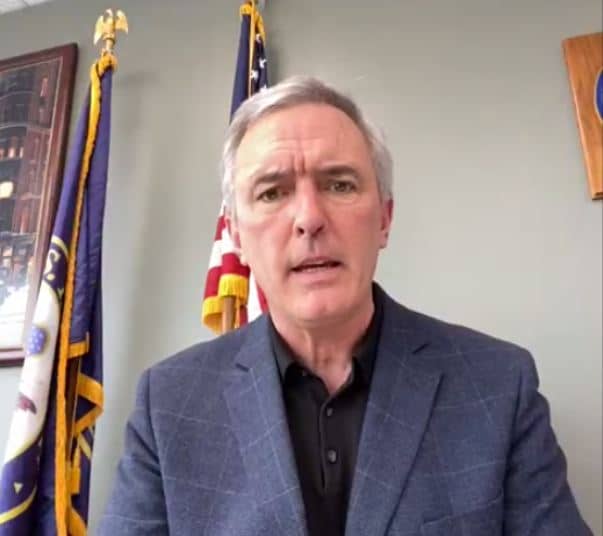
“This wasn’t the first kind of attack like this nor will it be the last,” said Rep. James Comer, R-Ky.
He described the SolarWinds computer breach as a military-style attack that should result in a U.S. counterattack “with the same resources as if the instrument of attack were physical or kinetic.”
“Kinetic” refers to the force of a blast generated by explosives.
SolarWinds Inc. is an Austin, Texas-based company that develops business software to manage information technology infrastructure. As of December 2020, its roughly 300,000 customers included nearly all Fortune 500 companies and numerous federal agencies.
On Dec. 12, SolarWinds discovered that one of its products called Orion was the target of a sophisticated hacker attack traced to Russia. The attack persisted undetected for nine months last year and invaded emails, source code and documents of the Department of Energy and other federal agencies.
Microsoft Corp. President Brad Smith called the computer breach “the largest and most sophisticated attack the world has ever seen.”
He told the House Oversight and Reform Committee that the attack invaded the software of about 17,000 SolarWinds customers, reaching deep into American technology companies and government agencies. One of them was Microsoft.
“This was an attack on the software supply chain,” Smith said.
He added, “It was the kind of act that was reckless. It was the kind of act that needs consequences.”
Unlike nearly any other time Microsoft has been investigated, he agreed a bigger role for the government was needed to protect American information technology infrastructure.
A team from the Russian Foreign Intelligence Service allegedly exploited an old loophole in Microsoft software to gain a backdoor into SolarWinds programs, then altered them so slightly it went unnoticed. The alteration turned off any firewalls that would prevent the Russians from monitoring how the programs were used by SolarWinds customers.
Some lawmakers accused SolarWinds of lax security, such as when one of its employees used the password SolarWinds123 to gain access to its servers.
Sudhakar Ramakrishna, SolarWinds’ chief executive officer, described as unrealistic beliefs that a private corporation could provide complete protection against such a sophisticated “nation-state” attack.
“They were very, very careful about covering their tracks,” Ramakrishna said.
He added, “All software has some sort of vulnerability or another.”
Among options Congress is considering is granting more authority to the Cybersecurity and Infrastructure Security Agency. It is a federal agency founded in 2018 that coordinates government cybersecurity with corporations, state and local governments and other infrastructure operators.
Although it is a small agency now, some lawmakers want it to become a major player in the nation’s cybersecurity.
They are considering legislation that would require companies and government agencies to share information about cyberthreats by using CISA as their clearinghouse. They would be required to promptly report attacks to CISA. The agency also would be likely to spearhead counter attacks against hackers.
Rep. John Katko, R-N.Y., who supports expanding CISA, said, “CISA still does not have the proper authorities … to nimbly respond to attacks.”
He described cybersecurity as an arms race when he said Russia, China, Iran and North Korea are “winning the modern-day arms race and we need to step up.”
Some of the corporate executives suggested more government funding for cybersecurity education to fill the estimated 300,000-job shortfall of qualified applicants.